Records Management is intended to help businesses manage security and data governance as more struggle to handle increased amounts of data and regulatory requirements. Microsoft today announced the general availability of Records Management in Microsoft 365, a new tool built to help businesses protect and manage sensitive data. Many struggle to create strong security, privacy, and risk capabilities, especially as the pandemic shifts operations. A new Harvard...
Read More
May 2020
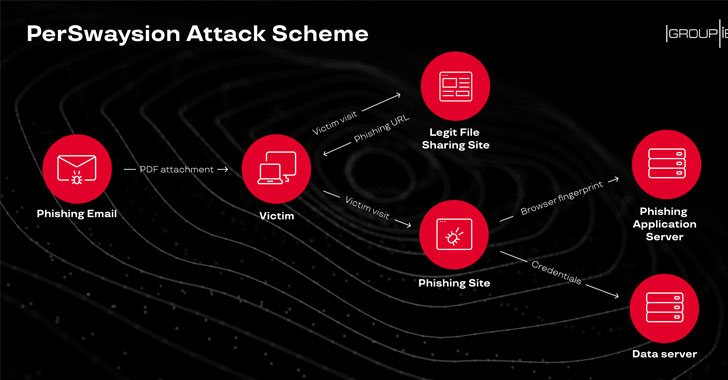
In the last few months, multiple groups of attackers successfully compromised corporate email accounts of at least 156 high-ranking officers at various firms based in Germany, the UK, Netherlands, Hong Kong, and Singapore. Dubbed 'PerSwaysion,' the newly spotted cyberattack campaign leveraged Microsoft file-sharing services—including Sway, SharePoint, and OneNote—to launch highly targeted phishing attacks. According to a report Group-IB Threat Intelligence team published today and shared with The...
Read MoreIn November 2019, the Australian Signals Directorate’s Australian Cyber Security Centre coordinated a national cyber security exercise series in partnership with Australia’s electricity industry and government agencies. The series involved two exercises, a 2-day operational exercise and a strategic discussion exercise. The exercises were designed to strengthen industry and governments’ coordinated response to a significant cyber incident affecting Australia’s electricity sector. Participants were from the electricity industry,...
Read MoreCybersecurity researchers from ESET said they took down a portion of a malware botnet comprising at least 35,000 compromised Windows systems that attackers were secretly using to mine Monero cryptocurrency.The botnet, named "VictoryGate," has been active since May 2019, with infections mainly reported in Latin America, particularly Peru accounting for 90% of the compromised devices."The main activity of the botnet is mining Monero cryptocurrency," ESET...
Read MoreA new malware campaign has been found using coronavirus-themed lures to strike government and energy sectors in Azerbaijan with remote access trojans (RAT) capable of exfiltrating sensitive documents, keystrokes, passwords, and even images from the webcam. The targeted attacks employ Microsoft Word documents as droppers to deploy a previously unknown Python-based RAT dubbed "PoetRAT" due to various references to sonnets by English playwright William Shakespeare. "The RAT...
Read MoreCybercriminals continue to target Australians through a range of COVID-19 themed scams, fraud attempts and deceptive email schemes, the Australian Cyber Security Centre (ACSC) has warned in a new threat update. Since 10 March 2020 the ACSC has: received more than 95 cybercrime reports about Australians losing money or personal information to COVID-19 themed scams and online frauds, responded to 20 cyber security incidents affecting COVID-19...
Read More'Mozi' combines code from three previously known IoT malware. Researchers at CenturyLink have found a new malware family that combines code from at least three other previously known malware to target Internet of Things (IoT) devices. Devices infected with "Mozi," as CenturyLink is calling the new malware, are being assembled into an IoT botnet that can be used to launch distributed denial-of-service (DDoS) attacks, for data exfiltration,...
Read More