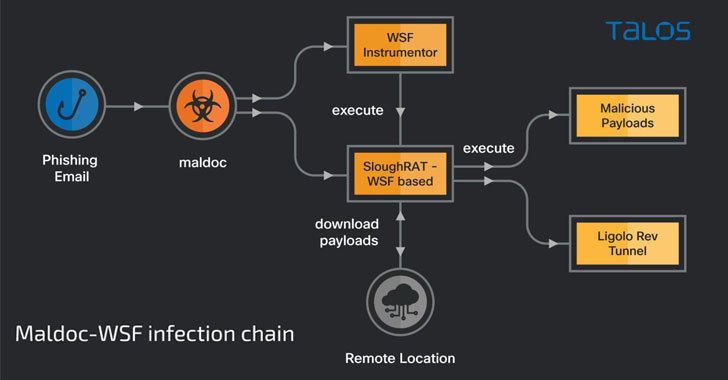
The Iranian state-sponsored threat actor known as MuddyWater has been attributed to a new swarm of attacks targeting Turkey and the Arabian Peninsula with the goal of deploying remote access trojans (RATs) on compromised systems. "The MuddyWater supergroup is highly motivated and can use unauthorized access to conduct espionage, intellectual property theft, and deploy ransomware and destructive malware in an enterprise," Cisco Talos researchers Asheer Malhotra,...
Read More
Cybersecurity
The hacker group that recently broke into systems belonging to graphics chip maker Nvidia has released two of the company's old code-signing certificates. Researchers warn the drivers could be used to sign kernel-level malware and load it on systems that have driver signature verification. The certificates were part of a large cache of files that hackers claim totals 1TB and includes source code and API documentation...
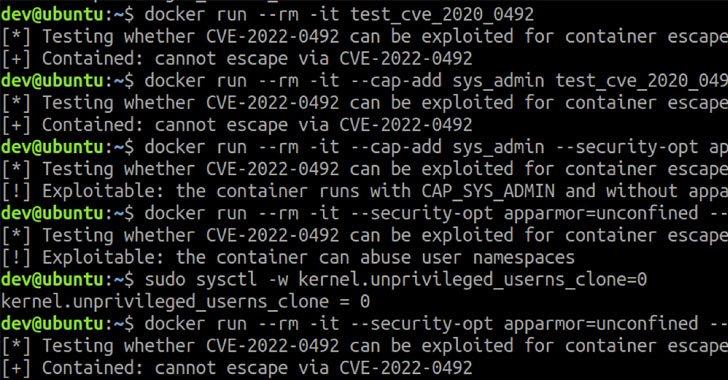
Read MoreDetails have emerged about a now-patched high-severity vulnerability in the Linux kernel that could potentially be abused to escape a container in order to execute arbitrary commands on the container host. The shortcoming resides in a Linux kernel feature called control groups, also referred to as cgroups version 1 (v1), which allows processes to be organized into hierarchical groups, thereby making it possible to limit and...
Read MoreThe Great Resignation hits every company hard, but it can be terrifying when your security pros leave in droves. There are more than the obvious risks at stake, and CISOs must manage them all. A checklist can help ensure mistakes aren't made and regrets aren't expensive. "As companies deal with increased rates of employee turnover, they must also consider the fact that highly skilled ex-employees are...
Read MoreA group of academics from Tel Aviv University have disclosed details of now-patched "severe" design flaws affecting about 100 million Android-based Samsung smartphones that could have resulted in the extraction of secret cryptographic keys. The shortcomings are the result of an analysis of the cryptographic design and implementation of Android's hardware-backed Keystore in Samsung's Galaxy S8, S9, S10, S20, and S21 flagship devices, researchers Alon Shakevsky,...
Read MoreThe Australian insurance industry is being inundated with rapidly changing customer expectations and demands with digital transformation a necessity for insurers to increase customer engagement, make claims processes easier, better serve employees and for competitive advantage. This increased reliance on digital technologies, as well as the sensitive data collected by insurance providers, have made the industry a prime target for cybercriminals. Insurance accounted for 34 of...
Read MoreSimilarities have been unearthed between the Dridex general-purpose malware and a little-known ransomware strain called Entropy, suggesting that the operators are continuing to rebrand their extortion operations under a different name. "The similarities are in the software packer used to conceal the ransomware code, in the malware subroutines designed to find and obfuscate commands (API calls), and in the subroutines used to decrypt encrypted text," cybersecurity...
Read MoreResearchers found an easy-to-exploit vulnerability in Snap, a universal application packaging and distribution system developed for Ubuntu but available on multiple Linux distributions. The flaw allows a low-privileged user to execute malicious code as root, the highest administrative account on Linux. The vulnerability, tracked as CVE-2021-44731, is part of a series of flaws that researchers from security firm Qualys found in various Linux components while investigating...
Read MoreMost organizations appear to be making little headway in addressing application security issues despite all of the heightened concerns around the topic, a new study shows. The study, by researchers at NTT Application Security, is based on data from some 15 million scans, mostly of Internet-facing Web applications at customer locations through 2021. Last year organizations took more than six months (193.1 days), on average, to...
Read MoreMicrosoft has warned of emerging threats in the Web3 landscape, including "ice phishing" campaigns, as a surge in adoption of blockchain and DeFi technologies emphasizes the need to build security into the decentralized web while it's still in its early stages. The company's Microsoft 365 Defender Research Team called out various new avenues through which malicious actors may attempt to trick cryptocurrency users into giving up...
Read More