Experts Find Strategic Similarities b/w NotPetya and WhisperGate Attacks on Ukraine
Latest analysis into the wiper malware that targeted dozens of Ukrainian agencies earlier this month has revealed “strategic similarities” to NotPetya malware that was unleashed against the country’s infrastructure and elsewhere in 2017.
The malware, dubbed WhisperGate, was discovered by Microsoft last week, which said it observed the destructive cyber campaign targeting government, non-profit, and information technology entities in the nation, attributing the intrusions to an emerging threat cluster codenamed “DEV-0586.”
“While WhisperGate has some strategic similarities to the notorious NotPetya wiper that attacked Ukranian entities in 2017, including masquerading as ransomware and targeting and destroying the master boot record (MBR) instead of encrypting it, it notably has more components designed to inflict additional damage,” Cisco Talos said in a report detailing its response efforts.
Stating that stolen credentials were likely used in the attack, the cybersecurity company also pointed out that the threat actor had access to some of the victim networks months in advance before the infiltrations took place, a classic sign of sophisticated APT attacks.
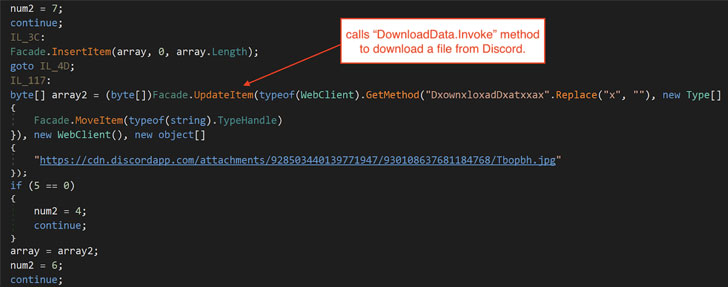
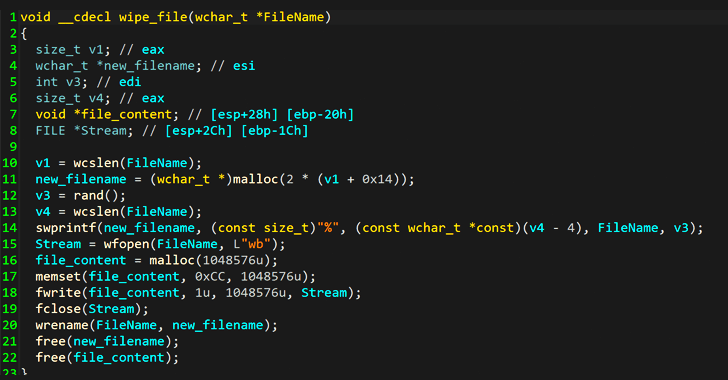
The WhisperGate infection chain is fashioned as a multi-stage process that downloads a payload that wipes the master boot record (MBR), then downloads a malicious DLL file hosted on a Discord server, which drops and executes another wiper payload that irrevocably destroys files by overwriting their content with fixed data on the infected hosts.
The findings come a week after roughly 80 Ukrainian government agencies’ websites were defaced, with the Ukrainian intelligence agencies confirming that the twin incidents are part of a wave of malicious activities targeting its critical infrastructure, while also noting that the attacks leveraged the recently disclosed Log4j vulnerabilities to gain access to some of the compromised systems.
“Russia is using the country as a cyberwar testing ground — a laboratory for perfecting new forms of global online combat,” Wired’s Andy Greenberg noted in a 2017 deep-dive about the attacks that took aim at its power grid in late 2015 and caused unprecedented blackouts.
“Systems in Ukraine face challenges that may not apply to those in other regions of the world, and extra protections and precautionary measures need to be applied,” Talos researchers said. “Making sure those systems are both patched and hardened is of the utmost importance to help mitigate the threats the region faces.”
Full article attribution is made to its original source and author.