Introducing ‘Secure Access Service Edge’
The industry’s latest buzzword is largely a repackaging exercise that bundles a collection of capabilities together and offers them as a cloud-delivered service.
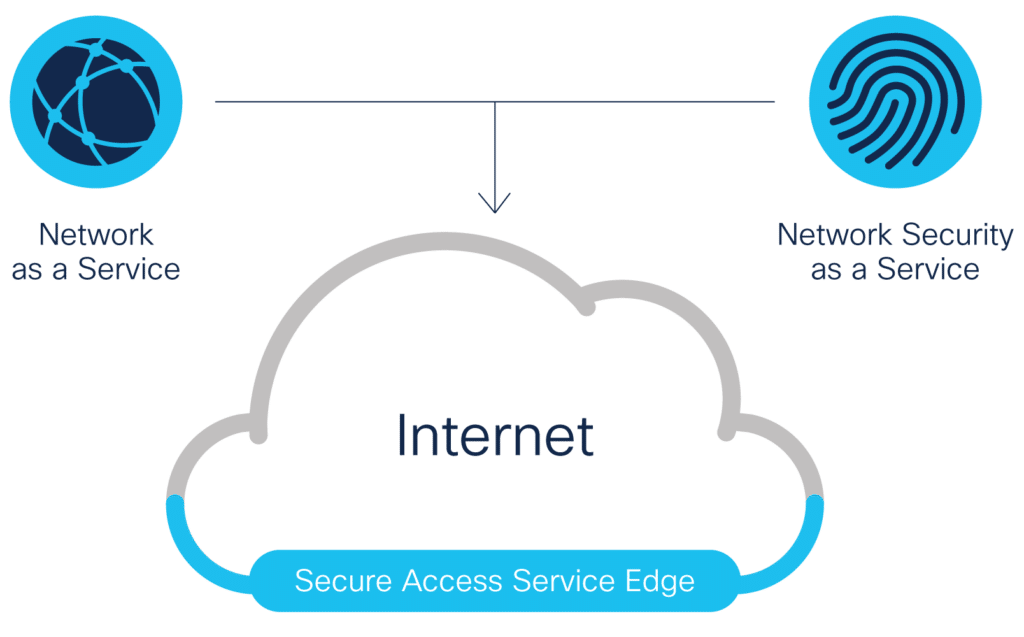
A new buzzword invading the marketing materials of cybersecurity vendors is Standing for Secure Access Service Edge (SASE). The term, coined by Gartner, refers to a technology trend in support of cloud-based applications and remote working, in which networking and security functionality converge in a single offering.
Omdia has its reservations about SASE as a product category, but we recognise that numerous vendors have adopted this parlance to describe all or part of their network security offerings.
The idea of SASE is attractive: that a single vendor, operating from the cloud, can offer an enterprise all its requirements for branch and remote employee networking, plus all the functionality to deliver that connectivity securely. On the networking side, this mainly covers functionality delivered by most software-defined wide area networking (SD-WAN) platforms, including:
- Dynamic WAN link management
- Multipath application steering and failover
- Quality of service
- Network-layer visibility and path monitoring
Meanwhile, in terms of security, a range of capabilities should be present, namely:
- Application-aware firewall (NGFW-like functionality)
- Secure web gateway (web traffic proxying)
- Cloud access security broker (CASB, delivering policy-based SaaS access management)
- Access control (VPN or zero-trust access)
An argument can be made for other subgroups here, such as data loss prevention (DLP), which many CASBs now include as a matter of course, as well as capabilities such as mobile device management (MDM) and decryption and inspection of encrypted traffic.
As such, it becomes clear that SASE is essentially a repackaging exercise, bundling a collection of capabilities together and offering them as a cloud-delivered service, almost certainly as a shopping list from which the customer can pick and mix individual features. While delivering traditionally on-premises-based networking and security capabilities from the cloud is significant, mode of delivery alone does not make SASE a new class of technology. As such, the term is reminiscent of UTM (unified threat management), an early 2000s-era term for multifunction security appliances sold for small businesses and branch offices. While SASE may serve to encapsulate an idea, it is an exercise in marketing rather than an advance in technology.
Reactions Vary from Enthusiasm to Skepticism
SASE is largely about mode of delivery and product marketing, which explains why it is so easy for different types of vendors to adopt SASE and apply it to their offerings. Omdia identifies at least three groups of vendors that have applied the SASE marketing concept to position their product offerings:
- Type 1. There are the top-tier cybersecurity, networking, and data center specialists, such as Palo Alto Networks, Akamai, VMware, and Zscaler, that have latched onto SASE as a “market” into which they can sell a subset of their overall portfolios. Several SD-WAN vendors are also in this group.
- Type 2. Those CASB vendors that were not acquired during the great landgrab in that space (Netskope, Bitglass, and CipherCloud) have generally embraced the term, albeit with differing degrees of enthusiasm.
- Type 3. Then there is a group of vendors that had been struggling to find an appropriate acronym for what they do. They can complement, or obviate the need for, an SD-WAN: OPAQ, NetFoundry, and Cato Networks are in this category. SASE provides a convenient peg on which to hang their respective hats.
For all this enthusiasm, however, SASE is not without its critics. Omdia’s Clifford Grossner has described it as “simply edge computing, connectivity, and security with integrated management,” and questioned whether enterprises would want to buy all this from a single supplier, since it means placing a sizable bet on just one technology provider.
There are those who have criticised the absence of analytics or machine learning for purposes of automating functionality from the basic set of capabilities. And while some in the vendor community have hailed SASE as “the future of SD-WAN,” others point to the evolution of SD-branch as the more likely route.
SASE Should Eventually Cede to Multimodal Solutions
There is little question that SASE is presently at or near the apex of its hype cycle. Omdia bases this both on anecdotal references to the term/acronym as well as recent market events. Of note are Palo Alto Networks’ recent $420 million acquisition of CloudGenix, largely driven by SD-WAN technology to bolster its Prisma SASE offering, as well as recently repositioned SASE vendor Cato Networks landing a new $77 million Series D round of venture capital funding. Clearly, vendors and investors alike see SASE-aligned solutions as an area of opportunity.
Perhaps the most helpful benefit SASE provides the marketplace is an easy-to-understand shorthand to describe a cloud-delivered solution set combining integrated networking and security functions. What was recently a somewhat obscure, hard-to-define concept for individual vendors to articulate suddenly becomes much faster to convey and easier to understand, particularly for those learning about the associated solution sets for the first time. This alone will unquestionably help facilitate adoption of SASE-aligned product offerings.
Despite the many benefits of cloud-delivered IT, SASE is merely the latest waypoint of an ongoing journey that will see continued evolution in the way cybersecurity technology is delivered. The rise of microservices-based and serverless architectures will again require security to be delivered through alternative means, likely as componentized functions within modular application architectures. The ongoing proliferation of Internet of Things (IoT) devices, most notably on the network edge, will drive growing need for IoT security functionality, delivered from the network edge in order to reduce IoT application latency and ensure bandwidth efficiency. Undoubtedly, other technologies that Omdia expects will become prominent in the coming decade — such as 5G, autonomous systems, and quantum computing — will further disrupt and change the way in which cybersecurity solutions are delivered.
Multimodal Requirements
Ultimately, Omdia sees most cybersecurity technology segments evolving toward a multimodal delivery paradigm. As digital transformation takes hold, enterprises will come to demand fluidity in how their cybersecurity technology is delivered, based on evolving business needs (a new branch office opens; another company becomes a subsidiary; a division is spun off and requires access to some applications during the transition; even perhaps a new strain of virus forces an entire business unit to work from home indefinitely…).
An increasing pace of change within enterprise IT means today’s need for cloud-delivered security may fluidly evolve into tomorrow’s need for security delivered on the edge or as componentized functions, and just as quickly revert back again. Enterprises can expect multimodal offerings that can be dynamically provided in a variety of delivery modes, with pricing and licensing to accommodate change on demand.
Full article attribution is made to its original source and author.

