New Chrome 0-day Bug Under Active Attacks – Update Your Browser Now!
Attention readers, if you are using Chrome on your Windows, Mac, and Linux computers, you need to update your web browsing software immediately to the latest version Google released earlier today.
With the release of Chrome 78.0.3904.87, Google is warning billions of users to install an urgent software update immediately to patch two high severity vulnerabilities, one of which attackers are actively exploiting in the wild to hijack computers.
Without revealing technical details of the vulnerability, the Chrome security team only says that both issues are use-after-free vulnerabilities, one affecting Chrome’s audio component (CVE-2019-13720) while the other resides in the PDFium (CVE-2019-13721) library.
The use-after-free vulnerability is a class of memory corruption issues that allows corruption or modification of data in the memory, enabling an unprivileged user to escalate privileges on an affected system or software.
Thus, both flaws could enable remote attackers to gain privileges on the Chrome web browser just by convincing targeted users into visiting a malicious website, allowing them to escape sandbox protections and run arbitrary malicious code on the targeted systems.
Google Chrome Zero-Day Under Active Attacks
Discovered and reported by Kaspersky researchers Anton Ivanov and Alexey Kulaev, the audio component issue in the Chrome application has been found exploited in the wild, though it remains unclear at the time which specific group of hackers.
“Google is aware of reports that an exploit for CVE-2019-13720 exists in the wild,” Google Chrome security team said in a
“Access to bug details and links may be kept restricted until a majority of users are updated with a fix. We will also retain restrictions if the bug exists in a third party library that other projects similarly depend on, but haven’t yet fixed.”
The use-after-free issue is one of the most common vulnerabilities discovered and patched in the Chrome web browser in the past few months.
Just over a month ago, Google released an urgent security update for Chrome to patch a total of four use-after-free vulnerabilities in different components of the web browser, the most severe of which could allow remote hackers to take control of an affected system.
In March this year, Google also released an emergency security update for Chrome after miscreants were found actively exploiting a similar use-after-free Chrome zero-day vulnerability in the wild affecting the browser’s FileReader component.
Technical Details of Chrome 0-day Exploit
A day after Google released an emergency patch update for Chrome browser to fix two high-severity vulnerabilities, cybersecurity firm Kaspersky Labs revealed more technical details about the one that it reported to Google and was spotted being exploited in the wild.
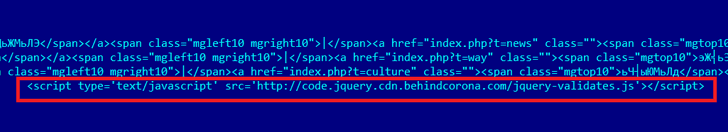
According to the researchers, attackers compromised a Korean-language news portal. They planted the exploit code on the site, like a watering-hole, to hack computers of its visitors opening the news portal using vulnerable versions of Google Chrome.
The exploit reportedly installs the first stage malware on the targeted systems after exploiting Chrome vulnerability (CVE-2019-13720), which then connects to a hard-coded remote command-and-control server to download the final payload.
Dubbed “Operation WizardOpium” by the researchers, the cyberattack has not yet been attributed to any specific group of hackers. Still, researchers found some similarities in the exploit code with the infamous Lazarus hacking group.
“So far, we have been unable to establish a definitive link with any known threat actors. There are certain very weak code similarities with Lazarus attacks, although these could very well be a false flag. The profile of the targeted website is more in line with earlier DarkHotel attacks that have recently deployed similar false flag attacks,” Kaspersky said.
For more details on the Operation WizardOpium exploiting the recently-patched Chrome vulnerability, you can head on to the new report just published by Kaspersky.
Patch Available: Update Google Chrome Immediately
To patch both security vulnerabilities, Google has already started rolling out Chrome version 78.0.3904.87 for Windows, Mac, and Linux operating systems.
Although the Chrome web browser automatically notifies users about the latest available version, users are recommended to manually trigger the update process by going to “Help → About Google Chrome” from the menu.
Besides this, Chrome users are also recommended to run all software on their systems, whenever possible, as a non-privileged user in an attempt to diminish the effects of successful attacks exploiting any zero-day vulnerability.
We will update you with more information about these security vulnerabilities as soon as Google releases their technical details.
Full article attribution is made to its original source and author.